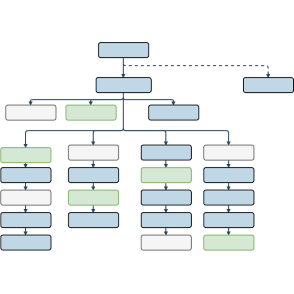
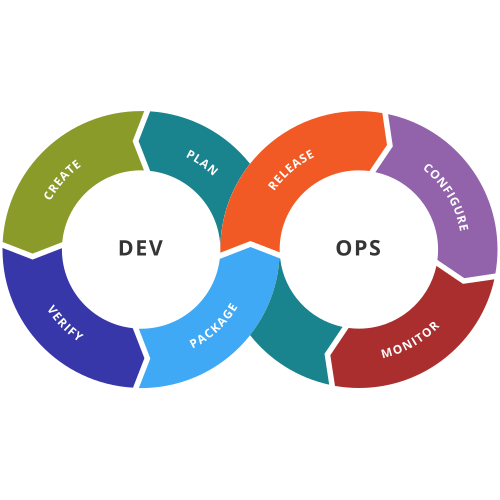
One of the key mindset changes needed for a successful DevOps transformation is to view software development as a continuous process, rather than a one-off project.
privileged mode and Nginx as a loadbalancer/proxy for allowing connections to the VPN server.